#Smart Contracts

AWS Integrates Chainlink to Power Blockchain Data
Amazon Web Services (AWS), the cloud computing division of Amazon, has integrated the data standards and services of the decentralized oracle network Chainlink into its platform, enabling connectivity between traditional cloud infrastructure and blockchain networks.
The integration, according to AWS, aims to address the blockchain oracle problem. Although blockchain networks operate as decentralized ledgers, they are not inherently designed to connect with external data sources, application programming interfaces (APIs), and other blockchains. This limitation presents a significant challenge for developers building digital asset solutions and tokenization products that depend on real-world data for operational efficiency.
By integrating Chainlink data standards into its marketplace, AWS addresses this connectivity problem, making it possible for blockchain networks to connect to its cloud infrastructure while maintaining the security, compliance, and reliability standards required by financial institutions.
The integration brings three Chainlink oracle services into the AWS Marketplace. These include Chainlink Data Feeds, which provide access to decentralized price and market data for asset valuation, assessment, and risk management; Chainlink Data Streams, which deliver fast and secure data that enables on-chain systems to respond to market movements in real time and manage risk dynamically; and Chainlink Proof of Reserve, which provides secure and verifiable on-chain reserve attestations for stablecoins and other tokenized assets.
Through this integration, enterprises will be able to build tokenization solutions that leverage AWS cloud capabilities alongside blockchain functionality without needing to independently solve the blockchain oracle problem. Developers will also be able to connect external data sources to blockchain applications through secure oracle networks while using AWS compute resources.
Platforms Integrate with Decentralized Oracle Networks
Decentralized oracle networks, which are blockchain-based middleware systems that securely bridge real-world data to blockchain networks using several independent nodes, have increasingly been integrated into platforms in recent times.
Just this month, Polymarket integrated Pyth Network into its prediction market platform. Through this integration, Polymarket enabled traders to place predictions on real-life commodities such as gold and silver, as well as U.S. stocks, including NVIDIA and Apple.
Allor Network, also this month, integrated the decentralized oracle network Band Protocol into its platform, allowing for the secure delivery of real-world data for its Web3 applications.
Chainlink decentralized oracles have also been integrated into traditional finance platforms, including SWIFT and SIX Group, the organization behind Switzerland’s principal stock exchange, the SIX Swiss Exchange, with plans underway to integrate them into the Australian Stock Exchange platform.

Ethereum Foundation Backs $1M Security Audit Program
The Ethereum Foundation has committed $1 million to subsidize smart contract security audits for developers building on Ethereum mainnet, a move that signals how seriously the organization is taking security as the network continues its push toward broader adoption. The initiative, called the Ethereum Security Subsidy Program, was announced April 14 on X and arrives at a time when the cost of professional audits has long been a sticking point for smaller teams trying to ship responsibly.
The program was built in partnership with digital asset advisory firm Areta, along with Nethermind and Chainlink Labs. Through Areta Market, the foundation is connecting builders with a pool of more than 20 vetted audit firms, including well-known names like Certora, BlockSec, Quantstamp, Spearbit, Sherlock, Zellic, Hacken, Cyfrin, Dedaub, Immunefi, and Nethermind Security. Rather than running a slow, confusing grant process, approved projects get subsidies applied directly through the platform, then request quotes, and can reportedly get them back within 48 hours.
How It Works
Builders submit applications through a form on Areta Market. From there, an Expert Committee, made up of representatives from the Ethereum Foundation, Areta, Nethermind, Chainlink Labs, and audit partners, reviews each submission. Selected teams can receive subsidies covering up to 30% of their total audit costs, with higher support possible on a case-by-case basis for certain projects. There is no fixed deadline for applications. The subsidy pool is distributed on a first-come basis until the $1 million is exhausted, with new cohorts picked every month.
The program is open to all Ethereum mainnet builders regardless of project size or development stage, though the foundation has said it will prioritize teams aligned with what it calls the CROPS principles: Censorship Resistance, Open Source, Privacy, and Security. The foundation published this framework just last month as part of a broader mandate defining its role and what it expects from builders in the Ethereum ecosystem.
Part of a Bigger Push on Security
This subsidy program did not come out of nowhere. It sits inside the foundation's broader Trillion Dollar Security Initiative, which launched last year and is explicitly focused on raising the network's security standards as Ethereum scales to handle more complex applications and larger sums of on-chain value. The thinking behind that initiative has always been that security infrastructure needs to grow alongside adoption, and audit access has been one of the more persistent gaps.
Areta CEO Fin Boothroyd framed the launch this way on X: the program is a joint initiative with top-tier audit providers, backed by an expert committee made up of leading voices from organizations that know Ethereum well. Notably, Areta ran a comparable $1 million audit subsidy for Solana developers prior to this, which gives the firm a useful blueprint for how these programs tend to play out in practice.
The Ethereum Foundation has been active on several fronts beyond this. In March 2026, it partnered with Morpho to expand its involvement in decentralized finance. In February, it rolled out Project Odin, a separate effort aimed at supporting teams building core infrastructure, particularly those that provide essential services but struggle to secure reliable funding. The audit subsidy program fits neatly into that broader pattern of trying to shore up the ecosystem before problems develop rather than after.
Wider Industry Context
The Ethereum Foundation is not alone in making these kinds of moves right now. Last month, Aave Labs announced a $1.5 million audit program focused specifically on securing the newly released Aave V4 protocol, another sign that some of the larger DeFi players are taking the cost-of-security problem seriously. The pattern emerging here looks like a coordinated, if informal, industry-wide shift toward treating security infrastructure as something worth investing in upfront.
Smart contract audits have always been considered a baseline best practice before deployment, yet for many teams, particularly earlier-stage ones, the cost has been prohibitive enough to skip or delay. If the program works as intended, more code gets reviewed before it goes live. That matters to the network given how much value is at stake on Ethereum at any given moment, and how frequently vulnerabilities in unaudited contracts have led to significant losses across DeFi.
There is still the question of whether $1 million is really enough to move the needle at scale. Audit costs vary widely depending on protocol complexity, and covering 30% of fees, while helpful, still leaves a meaningful share of the bill on the builder. The foundation has left the door open to higher support for select projects, which suggests it knows the ceiling matters. For now, the program represents a concrete, operational step rather than just a policy statement, and that puts it ahead of most security initiatives that never get past the announcement stage.

Hyperbridge Hack Leads to $237K ETH Loss on Ethereum
Hyperbridge, a cross-chain interoperability protocol built on Polkadot, was recently hit by a hack that led to the loss of approximately 108.2 ETH, roughly $237,000.
The attack, which occurred in the early hours of Monday, was caused by the exploitation of a smart contract vulnerability in the protocol’s token gateway contract on Ethereum.
By taking advantage of this vulnerability, the attacker forged a cross-chain message and proof that allowed them to bypass the Merkle proof verification of Hyperbridge’s Ethereum HandlerV1 contract. As this contract is central to security and proof verification on Hyperbridge’s Ethereum side, the attacker was able to gain unauthorized administrative control over the bridged DOT token contract on Ethereum.
With this administrative authority, the attacker minted approximately one billion fake bridged DOT tokens in a single transaction. The tokens were then immediately dumped into various liquidity pools through Uniswap V4 and other crypto aggregators such as Odos. However, due to poor liquidity and limited trading activity for the bridged DOT token on Ethereum, the attacker was only able to extract about 108 ETH, valued at roughly $237,000.
Polkadot acknowledged the incident in a statement on its official X account, noting that it was aware of the situation. The team stated that the breach only affected DOT tokens on Ethereum, and confirmed that its native DOT cryptocurrency, as well as DOT bridged through other platforms, remained unaffected.
To contain the issue, Hyperbridge temporarily paused the protocol. Seun Lanlege, founder of Polytope Labs, the team behind Hyperbridge, stated that the issue was under investigation shortly after the incident occurred.
Hyperbridge April Fool Joke
The Hyperbridge hack comes shortly after the team made an April Fool's joke on the 1st of April about being hacked, dismissing the idea as a joke and boasting that the protocol was unhackable, a move that sparked criticism about the team’s overconfidence.
Lanlege, the protocol’s founder, was also called out, with some in the crypto community accusing him of ignoring and rejecting security feedback and tests from white hat researchers who had identified flaws in the protocol’s security system.
The Hyperbridge exploit is one of almost 10 smart contract vulnerability exploits we have seen this year. In January, DeFi protocol Truebit and decentralized exchange aggregator Swapnet were hit by smart contract vulnerability exploits that led to the loss of approximately 26.4 million dollars and $13.4 million, respectively.
Solv Protocol and CrossCurve were also hit in the following months by smart contract vulnerability exploits. So far, over $400 million has been lost to crypto-related hacks and exploits this year.

Toss Eyes Blockchain Network and Native Crypto Token
South Korean fintech and payment company Toss is reportedly considering the launch of its own blockchain network and a native cryptocurrency token for its payment and financial services.
While preparations had already begun, Blockmedia, one of South Korea’s leading cryptocurrency media outlets, reports that the firm has not yet decided whether to launch a Layer 1 or Layer 2 blockchain, as decision-making has been paused amid delays in some compliance discussions.
By launching its own blockchain, Toss would be building a solid infrastructure for its super app, enabling the integration of several blockchain features, including on-chain finance, scalability, and smart contracts, into its existing payment system.
Toss: A Crypto-Friendly Fintech Platform
Despite operating mostly in the traditional finance space and amassing over 30 million registered users, about 60 percent of the population of South Korea, Toss has long been taking several pro-blockchain and crypto-friendly steps.
In June 2025, Toss, through its Stablecoin Task Force led by Chief Business Officer Kyuha Kim, filed 24 stablecoin applications with the Korean Intellectual Property Office, the country’s trademark and patent authority, securing stablecoin names including TOSSKRW. During the same period, Toss Bank, its banking subsidiary, submitted 48 additional stablecoin-related applications.
These efforts were part of Toss’s broader strategy to establish a position in South Korea’s crypto sector as a potential issuer of Korean won-backed stablecoins. The company also began recruiting blockchain engineers to advance this initiative.
In March 2026, at the Seoul Blockchain Meetup Conference in Seoul, Toss unveiled its Money 3.0 vision, which it describes as the next era of money.
According to Toss, this vision leverages blockchain and stablecoins to build a digital money system that combines programmability, borderless transactions, and composability, extending beyond the physical cash era of Money 1.0 and the electronic fiat money era of Money 2.0.
At the same event, Toss publicly announced plans to issue and distribute its Korean won-backed stablecoin.
Despite recent regulatory pressure on non-compliant cryptocurrency exchanges in South Korea, several fintech companies and banking institutions in the country, including Toss, have continued to adopt and integrate blockchain technology into their systems.
KakaoPay, a major domestic fintech company, recently joined the Coinbase-led x402 Foundation, a move that suggests potential future integration of blockchain technology into its payment systems. In addition, around eight domestic banks formed a consortium last year to jointly explore issuing Korean won-backed stablecoins.

Solana Foundation Moves To Strengthen Its Ecosystem Security
The Solana Foundation, in collaboration with blockchain security firm Asymetric Research, has launched new security initiatives aimed at strengthening the security of the Solana network.
In a blog post on Monday, the foundation announced the launch of new security initiatives designed to provide an extra layer of protection for protocols built on the network. Among these initiatives are STRIDE, a security framework, and SIRN, a network of security firms focused on protecting the Solana ecosystem.
The STRIDE Framework
STRIDE, which stands for Solana Trust, Resilience and Infrastructure for DeFi Enterprises, is a structured security framework and program launched by the Solana Foundation. It is aimed at evaluating, monitoring, and escalating security across all projects built on the Solana network.
The STRIDE framework is built on eight key pillars: program security, governance and access control, oracle and dependency risk, infrastructure security, supply chain security, operational security, monitoring and incident response, and log management and forensics.
These pillars will be used by the foundation’s partner, Asymmetric Research, to evaluate the security strength of all protocols on the Solana blockchain. Protocols with a total value locked of more than $10 million that pass the STRIDE evaluation will receive continuous operational security and active threat monitoring, funded by Solana Foundation grants. The higher the evaluation result, the greater the level of protection and funding they will receive.
Protocols with a total value locked of more than $100 million that pass the STRIDE evaluation will also receive, in addition to grants, formal fund verification. The foundation describes this as a mathematical, proof based method that exhaustively guarantees the correctness of smart contracts.
The findings of the STRIDE framework will be published publicly. According to the foundation, this is intended to give users and investors insight into the protocols they use and rely on.
SIRN: A Network of Security Firms
Among the initiatives launched by the Solana Foundation is SIRN, short for Solana Incident Response Network, a network of security firms that will respond and act in the event of a security incident.
Although SIRN will be available to all blockchain protocols on the Solana network, priority will be given to protocols with higher total value locked, similar to the additional benefits that protocols with higher total value locked will receive under the STRIDE program.
Interested in knowing who makes up SIRN?
The Solana Incident Response Network comprises Asymmetric Research, OtterSec, Neodyme, Squads, and ZeroShadow, a combination of cybersecurity firms that includes Web3 and traditional security firms as well as a smart contract auditing firm.
Increase in DeFi attacks
The programming initiatives launched by the Solana Foundation are in response to the over $280 million attack on Drift Protocol, the largest decentralized perpetual exchange on the Solana blockchain. The attack is, so far, the most devastating DeFi attack this year and the second largest in the history of the Solana blockchain, following the 2022 Wormhole attack, which resulted in losses exceeding $325 million.
Step Finance, a DeFi aggregator built on Solana, was also affected by a DeFi hack earlier this year, which led to losses of about $40 million. According to DeFiLlama, over $168 million was stolen across 34 blockchain protocols in the first quarter of this year, prior to the Drift incident.

Balancer Labs Shuts Down After $116M DeFi Hack
Balancer Labs, the core team behind the decentralized finance (DeFi) protocol Balancer, has announced plans to wind down after a $116 million exploit that occurred in November.
The decision, according to CEO Marcus Hardt, was driven by the impact of the hack. Despite continuing to generate revenue, Balancer Labs’ economic model was no longer sustainable in the aftermath of the hack.
“We were spending too much to attract liquidity relative to what that liquidity was actually generating in revenue,” Hardt said. “We were diluting BAL holders to sustain a system that, in my view, was no longer serving the protocol well. At some point, you have to be honest about that.”
With Balancer Labs winding down its operations, the protocol is expected to be managed by the Balancer Foundation and its decentralized autonomous organization (DAO), an approach supported by co-founders Hardt and Fernando Martinelli.
DAO members have been asked to vote on a proposal to restructure the protocol and its tokenomics. If approved, BAL emissions will end, all fees will be routed to the treasury, and the protocol’s share of swap fees will be reduced. The team size will also be cut.
So, while Balancer Labs, the core development team, is winding down, the protocol will continue operating under new management with a leaner structure.
The Balancer Protocol Exploit
On November 3, 2025, Balancer Protocol suffered a smart contract exploit targeting its V2 composable stable pools, resulting in the theft of significant amounts of cryptocurrency.
Although Balancer had a permission system in place, a bug in the smart contract allowed the attacker to bypass these controls. The attacker exploited the vulnerability to gain unauthorized access to the protocol’s shared vault system, enabling them to drain assets from multiple liquidity pools across different blockchains simultaneously.
The hack had a severe impact on Balancer, causing its total value locked (TVL) to drop from about $775 million to $258 million within days of the exploit, according to a report. Its native token, BAL, also fell by about 30%.
The shutdown of the Balancer Labs team comes weeks after crypto aggregator Step Finance announced its own shutdown following a January 31 hack that reportedly led to losses of between $26 million and $40 million from the protocol’s treasury.
Bunni, a decentralized liquidity protocol built on Uniswap V4, also shut down around October last year after suffering a hack that resulted in losses of about $8.4 million.

A Ghost From Ethereum’s Past Is Becoming a $220 Million Security Fund
Nearly a decade after one of crypto’s most painful episodes, a large pool of forgotten Ether tied to TheDAO is being put back to work. This time, not as a risky experiment, but as a long-term security fund for Ethereum.
Roughly $220 million worth of ETH that has sat unclaimed since the infamous 2016 DAO hack is being transformed into a new, ecosystem-wide security endowment. The goal is simple on paper: fund audits, tools, research, and emergency response efforts that help keep Ethereum and its users safe.
From Crisis to Capital
To understand why this matters, you have to go back to TheDAO itself.
In early 2016, TheDAO was pitched as a radical idea. A decentralized venture fund governed entirely by code and token holders. It quickly became the biggest crowdfunding event crypto had ever seen, pulling in millions of Ether from participants around the world.
Then it broke.
A flaw in the smart contract allowed an attacker to drain a massive portion of the funds. Panic followed. Debates erupted. And eventually, Ethereum hard-forked to reverse the damage, a decision that permanently split the network and created Ethereum Classic.
What was left behind were fragments of that original system. Contracts that never got emptied. ETH that was never claimed. Funds that, for years, were largely ignored.
Now they are coming back into focus.
Where the Money Comes From
The new security fund is built from two main pools of ETH left over from TheDAO era.
The largest portion comes from what is known as the ExtraBalance contract. This Ether was left behind during the original refund process, largely due to overpayments and technical quirks. Today, that balance adds up to more than 70,000 ETH, worth over $200 million at current prices.
Most of that ETH will not be spent outright. Instead, the majority is expected to be staked, generating yield that can fund security work year after year. That turns a one-time windfall into something closer to an endowment.
The second pool is smaller but more immediately usable. Around 4,600 ETH sits in old curator-related wallets connected to TheDAO. Those funds are expected to be deployed more directly toward grants and security initiatives.
Together, they form one of the largest dedicated security funds the Ethereum ecosystem has ever seen.
What the Fund Will Actually Do
Ethereum has no shortage of capital, but security spending has often been fragmented. This fund is meant to change that.
The focus is broad by design. Audits for major protocols. Funding for security tooling and infrastructure. Support for incident response teams when exploits happen. Research into emerging risks across layer 2 networks, wallets, and user-facing applications.
There is also an emphasis on user protection, things like phishing detection, transaction safety tools, and services that help everyday users avoid costly mistakes.
Some of the money will likely go to well-known security firms. Some will go to smaller, community-driven projects that quietly do important work but struggle to secure consistent funding.
Governance, DAO-Style
In a nod to TheDAO’s original vision, the fund will not operate like a traditional foundation grant program.
Instead, distribution is expected to lean heavily on decentralized governance mechanisms. Quadratic funding, retroactive grants, and community voting will all play a role. The idea is to reward impact, not just proposals, and to let a broad set of stakeholders help decide where the money goes.
The Ethereum Foundation will still be involved, particularly in setting guardrails and defining what qualifies as security work. But the ambition is to keep decision-making as open and participatory as possible.
Why This Matters Now
Ethereum is no longer an experimental network. It secures hundreds of billions of dollars in value across DeFi, NFTs, stablecoins, and layer 2 systems. With that scale comes constant pressure from attackers.
Exploits today are faster, more complex, and often more damaging. At the same time, public funding for security work tends to lag behind growth. This fund helps close that gap.
It also reflects a broader shift in how the Ethereum community thinks about risk. Security is no longer something you bolt on at the end. It is infrastructure.
The Bottom Line
There is something poetic about this moment. I love how they are taking one of Ethereum's darkest moments and turning it in to a security fund to try to ensure that something like this would never happen again.
TheDAO hack forced Ethereum to confront its own limits
It exposed the dangers of unaudited code and untested governance. It shaped how the ecosystem thinks about security to this day.
Turning the remnants of that failure into a permanent security fund feels like closing a loop. A way of acknowledging the past without being defined by it.
If the fund works as intended, one of crypto’s earliest disasters may end up funding its future resilience.

Midnight Launches December 8, A New Era of Privacy For Blockchain
Midnight, A New Era Of Privacy For Blockchain

On December 8, Midnight finally goes live. This is the moment the industry has been waiting for. Midnight is not just a new chain and not just another project. It is a fully engineered, zero knowledge powered data protection network that brings real confidentiality to blockchain without sacrificing compliance, security or transparency.
The launch of Midnight marks the beginning of a new era where individuals, developers and global enterprises can use blockchain without exposing everything to the public. Midnight introduces a rational privacy that is programmable, auditable and built for long term scale. There is nothing else like it in the market.
What Makes Midnight So Powerful
Midnight solves the problem that has limited every major blockchain from reaching full global adoption. Public ledgers reveal personal data, business logic, financial activity and sensitive operations. This stops enterprises from deploying real systems on chain. Midnight flips that limitation into strength.
Developers can create smart contracts with confidential logic, private state updates and selective disclosure. Midnight lets you reveal only what is required while keeping everything else shielded through zero knowledge proofs, enabling real-world application.
Because of its privacy centric architecture, Midnight unlocks use cases that have never been possible at scale.
-
Private decentralized finance
-
Confidential business workflows
-
Secure identity systems
-
Tokenized documents and assets with controlled access
-
Encrypted supply chain data
-
Private DAO voting
-
Permission controlled data sharing between institutions
Midnight is built specifically for these high value industries. This is why the launch tomorrow is so significant, a production ready privacy network designed for global use.
The December 8 launch is only the beginning of Midnight’s long term vision. Midnight is following a structured, multi phase roadmap that gradually increases capability, decentralization and real world utility. Each phase expands the network in a controlled and secure way, ensuring that privacy and identity features scale responsibly.
Below is a clear breakdown of Midnight’s roadmap based on the official announcement.
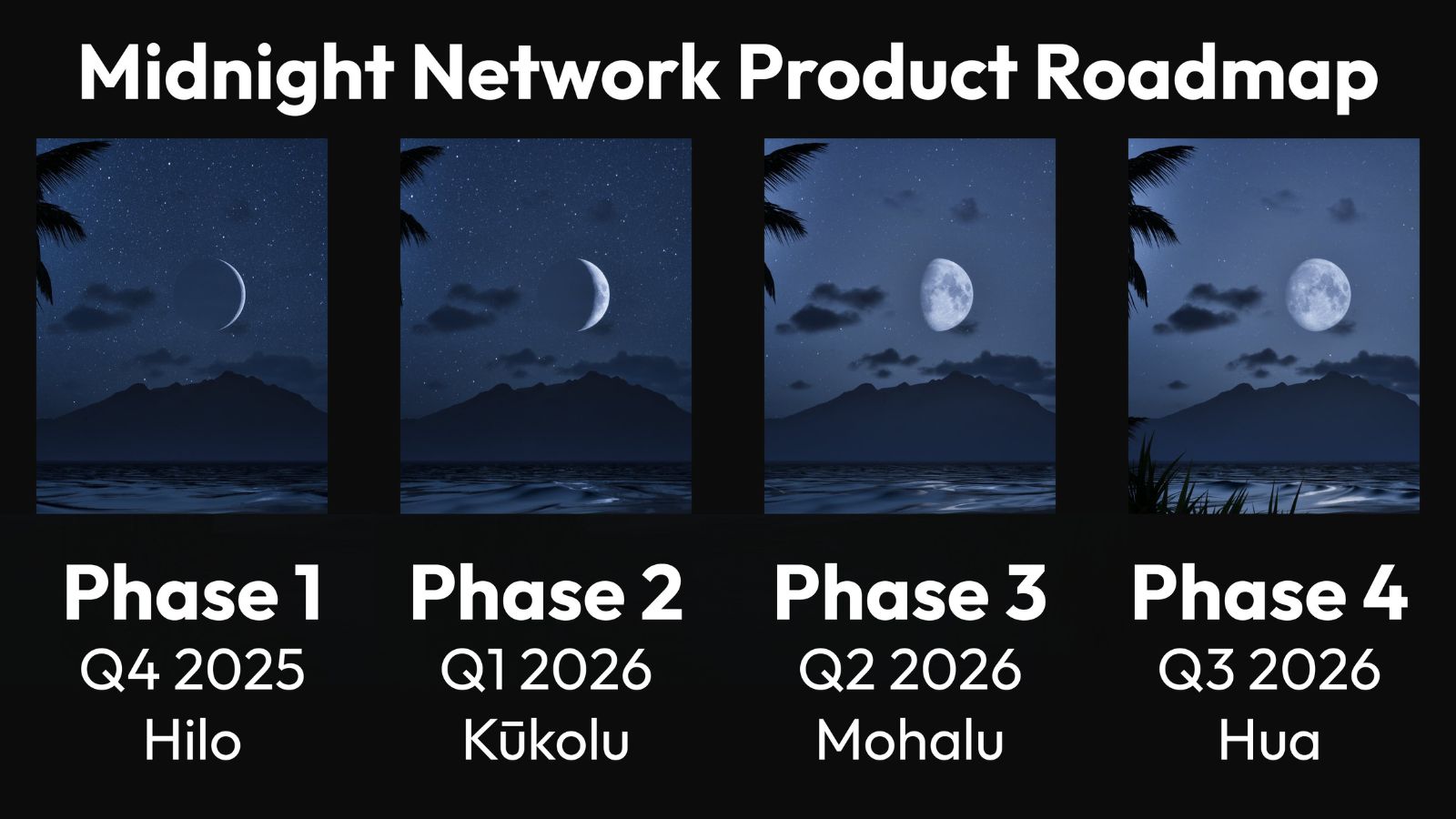
Phase 1: Hilo
Launch and Token Liquidity
This is the phase that begins with the December 8 activation of the Midnight network. Midnight becomes a live, operational chain with NIGHT available as a liquid asset.
Key elements of Phase 1:
-
Network activation and operational readiness
-
NIGHT becomes tradable and usable
-
Early participants, wallets and partners join the ecosystem
-
The foundation is set for developers to begin exploring Midnight’s capabilities
Hilo marks the transition from development into a functioning privacy network that users and builders can interact with directly.
Phase 2: Kūkolu
Federated Mainnet and Privacy Enabled Applications
During this stage, Midnight moves from initial activation into a federated mainnet operated by a combination of foundation validators and trusted partners. This creates a controlled yet fully functional environment for deploying real applications.
Highlights of Phase 2:
-
Federated mainnet with a secure validator set
-
Launch of the first privacy enabled DApps using Midnight’s zero knowledge architecture
-
Real applications begin leveraging features such as selective disclosure, private state, confidential identity and shielded computation
This is where Midnight shifts from infrastructure into a true application platform. Developers begin delivering privacy focused solutions that cannot be built on transparent chains.
Phase 3: Mōhalu
Network Scaling, Increased Participation and the Capacity Market
Mōhalu expands Midnight toward broader community participation. Block production begins opening up to more operators and the network starts preparing for full decentralization.
Core advancements in Phase 3:
-
Wider validator participation including future stake pool operators and community nodes
-
Stress testing and economic validation of the network
-
Activation of the DUST capacity exchange that powers private computation
-
Community involvement in testing scalability, privacy performance and governance mechanisms
This phase transforms Midnight from a limited validator model into an emerging decentralized network with a functioning economic system based on NIGHT and DUST.
Phase 4: Hua
Full Decentralization, Hybrid DApps and Cross Chain Privacy
Phase 4 represents the full maturity of Midnight. The network completes its transition into a decentralized, community governed privacy platform.
Key outcomes of Phase 4:
-
Complete decentralization of block production
-
NIGHT holders govern the network through on chain voting and proposal systems
-
Support for Hybrid DApps that integrate Midnight’s privacy layer into other chains and platforms
-
Cross chain interoperability where other networks can use Midnight as a privacy and identity service
At this stage, Midnight becomes not only a standalone privacy chain but also a universal privacy infrastructure for the broader blockchain industry.
Midnight Brings a New Dawn For Cardano
Even though Midnight is its own network, it operates as a data protection partner chain anchored to Cardano. This creates enormous value for ADA holders, Cardano developers and the entire ecosystem.
Cardano becomes the only major blockchain ecosystem with a production level privacy chain that remains regulation friendly. This is a massive competitive advantage. Cardano can now serve transparent applications and private applications without compromising security.
NIGHT is a Cardano native asset. Anyone who wants to use Midnight must interact with the Cardano ecosystem. This brings new wallets, new users, new liquidity and new developers directly into Cardano from multiple external ecosystems.
Cardano is now positioned as a realistic option for industries that need confidentiality. Finance, healthcare, supply chain, identity, enterprise management systems. These businesses can use Midnight for private computation while relying on the stability and settlement layer of Cardano.
Cardano has always focused on research, formal methods and sustainable architecture. Midnight takes that foundation and adds a powerful privacy dimension. This is the kind of advancement that reshapes how the industry sees Cardano.
Midnight is not a side project. It is a core evolution of the ecosystem.
How to Claim Your NIGHT Tokens
If you earned NIGHT through the Midnight distribution, the process to claim and redeem your tokens is straightforward once you know what to expect.
Step 1: Make Your Claim
Start by heading to the official Midnight Claim Portal. You will be asked for two things.
Your origin address
This is the address from the chain where you qualified. It might be a Cardano address or it could be from another supported chain like Bitcoin, Ethereum, Solana, XRP, BNB, Avalanche, or BAT. Midnight uses this to verify that you were eligible at the snapshot.
Your destination address
This is your Cardano wallet where you want to receive your NIGHT tokens. Any supported Cardano wallet works, as long as it is one you personally control.
Once both addresses are entered, you will need to accept the terms and sign a short verification message. This proves you actually own the origin address. After you submit everything, your NIGHT allocation is officially claimed and locked in the system.
Step 2: Wait for Your Tokens to Thaw
This is where Midnight does things a little differently. Your tokens do not unlock all at once. Instead, your allocation gradually thaws over a 360 day schedule. Midnight splits your total amount into four equal parts and each one unlocks roughly every ninety days.
The first unlock happens at a random time somewhere in the first ninety days after you claim. After that, each remaining quarter unlocks in sequence. It is a slow and steady release rather than a single burst, which helps keep the ecosystem healthy during the first year.
Step 3: Redeem the Unlocked Portion
Once your first portion has thawed, you can redeem it right away.
Go back to the Claim Portal, choose the unlocked portion and confirm the redemption. Your Cardano wallet will ask you to approve a small transaction fee. After the transaction goes through, your NIGHT tokens will appear in your wallet under the correct policy ID.
You can redeem each portion as it unlocks or wait until the end and redeem everything at once. It is entirely up to you.
Step 4: Do Not Miss the Grace Period
When the main redemption window ends, Midnight gives everyone an additional grace period to collect anything they have not redeemed yet. It is always best to stay on top of your thaw schedule, but the grace period gives you a buffer in case you miss something.
Once that time expires, collecting unredeemed tokens becomes a much more manual process, and it is not something you want to deal with if you can avoid it.
A Few Helpful Tips
-
Always use the official Midnight Claim Portal, not third party links.
-
Make sure your origin address comes from a wallet you control, since you need to sign the verification message.
-
Keep a bit of ADA in your Cardano wallet so you can cover redemption fees.
-
Double check your destination address before submitting. It is worth the extra moment.
Midnight Changes Everything
Midnight is not launching as an experiment. It is launching as a fully engineered, privacy centric blockchain ready for real adoption. December 8 is the beginning of a network built for global scale and long term impact.
Midnight brings confidential smart contracts into the mainstream. It gives developers the tools they have needed for years. It gives institutions a way to embrace blockchain without risking sensitive data. It gives Cardano a massive new frontier for growth.
Most of all, Midnight shows the world that privacy and transparency can work together. The chain is built to protect people, empower businesses and open the door to applications that were never possible before.
This is the start of a major shift in the industry. Midnight is ready. December 8 is the breakthrough moment.
Stay Connected
You can stay up to date on all News, Events, and Marketing of Rare Network, including Rare Evo: America’s Premier Blockchain Conference, happening July 28th-31st, 2026 at The ARIA Resort & Casino, by following our socials on X, LinkedIn, and YouTube.

Balancer Faces Over $110 Million in Outflows After Potential Exploit
Balancer Faces Over $110 Million in Outflows After Potential Exploit
The decentralized finance (DeFi) protocol Balancer is facing scrutiny after more than $110 million in assets were drained from its pools in what appears to be a large-scale exploit. Early reports surfaced from blockchain analysts, including @AdiFlips on X, who tracked the initial transactions and raised alarm over millions of dollars in outflows from Balancer’s smart contracts.
What Happened
Balancer’s smart contracts began showing suspicious transactions involving Wrapped Ether (WETH), Lido staked Ether (wstETH), and Origin staked Ether (osETH) on October 30. According to on-chain data shared by @AdiFlips, the transactions originated from Balancer’s “manageUserBalance” function, a part of its V2 smart contract system that handles user funds and pool accounting.
In just a few minutes, an unknown address moved more than $70 million worth of assets across multiple transactions. Follow-up analysis by several DeFi monitoring platforms later confirmed that total outflows exceeded $110 million, with funds being consolidated into a single wallet.
What the Analyst Found
On X, @AdiFlips posted the first thread highlighting the exploit, noting that the “manageUserBalance” function was being abused. He showed that the attacker was able to call the function in a way that bypassed standard permission checks, allowing them to drain funds from liquidity pools without ownership validation.
In his breakdown, he wrote:
“It looks like the Balancer exploit is real. Someone managed to bypass
msg.sendervalidation in themanageUserBalancefunction, allowing them to transfer tokens directly. Funds are being drained quickly.”
His real-time tracking of the attacker’s wallet provided the first public warning to liquidity providers (LPs), prompting many to start pulling funds before further losses.
Balancer’s Response
Balancer confirmed the issue shortly after the exploit began, posting an update on X:
“We are aware of a potential exploit impacting Balancer V2 pools. Our engineering and security teams are investigating with high priority.”
The team said it has contacted major blockchain security groups and forensic analysts to trace the funds and assess the exploit’s scope. Balancer has also offered a 20% white-hat bounty for the return of the stolen assets, promising leniency if the attacker cooperates.
If the funds are not returned within 48 hours, Balancer stated it would pursue the matter through law enforcement and deeper blockchain forensics, including cross-referencing IP, ASN, and timestamp data linked to on-chain activity.
How the Exploit Worked
Preliminary technical analysis suggests the attacker exploited a logic flaw in Balancer’s contract validation process. Specifically, they were able to manipulate the manageUserBalance function, which is responsible for handling deposits and withdrawals.
Normally, the function should only execute balance changes initiated by the user calling the transaction. However, a missing or incorrect sender check may have allowed the attacker to impersonate users and withdraw assets from shared liquidity pools.
This kind of bug falls under the category of access control vulnerabilities, a recurring issue in complex DeFi protocols that handle multiple users’ funds through permissioned functions.
Impact on Users
The exploit affects liquidity providers (LPs) participating in Balancer V2 pools, particularly those containing wrapped and staked Ethereum assets. If you are a Balancer LP, you should:
-
Check your wallet and pool exposure immediately.
-
Exit vulnerable pools until Balancer issues a full post-mortem.
-
Avoid interacting with any unverified Balancer contracts during the investigation period.
Balancer has not yet confirmed whether all funds can be recovered, but the incident has already shaken confidence in one of DeFi’s longest-running automated market makers.
Industry Reaction
The broader DeFi community reacted quickly. Security researchers and analysts echoed @AdiFlips’ findings, noting that the exploit underscores a recurring challenge in smart contract design. Small logic errors in permission validation can lead to massive financial losses.
Developers from other major protocols, including Curve and Uniswap, have reportedly reviewed similar functions in their contracts to ensure they are not exposed to the same vulnerability.
Meanwhile, crypto security firms have begun tracking the attacker’s wallet movements, which show small transfers through decentralized exchanges, possibly testing laundering routes or trying to break traceability before moving funds to privacy protocols.
Why This Matters
Balancer’s exploit is not just another DeFi hack. It is a reminder that code complexity equals risk, even for mature platforms. Balancer has handled billions in total value locked (TVL) since launching in 2020, making this one of the largest potential breaches in its history.
The event highlights three broader trends in DeFi:
-
Smart contract logic flaws remain a top vulnerability, even after audits.
-
Real-time community alerts like those from @AdiFlips play a crucial role in limiting damage.
-
Protocol accountability and transparency are now as important as code security itself.
What Happens Next
Balancer’s team is expected to publish a full incident report once its investigation concludes. They will likely propose governance measures to patch affected contracts and possibly establish compensation paths for liquidity providers who lost funds.
For now, on-chain watchers continue to track the exploiter wallet, which still holds tens of millions in Ether and related assets. Whether this turns into a partial recovery or another unsolved multimillion-dollar DeFi theft remains to be seen.
Final Thoughts
This exploit shows that even well-established DeFi protocols remain vulnerable to subtle design flaws. While Balancer’s prompt communication and bounty offer were commendable, the event reinforces the need for constant contract monitoring, active audits, and responsible disclosure systems across the sector.
For users, the lesson is simple: DeFi rewards innovation, but it still carries risk. Stay alert, follow verified analyst updates, and never assume any protocol is too established to be exploited.
Stay Connected
You can stay up to date on all News, Events, and Marketing of Rare Network, including Rare Evo: America’s Premier Blockchain Conference, happening July 28th-31st, 2026 at The ARIA Resort & Casino, by following our socials on X, LinkedIn, and YouTube.